Microcorruption: Sydney
Summary
This is a write-up of my solution to the Microcorruption CTF challenge "Sydney" (LOCKIT PRO r a.02).
Let's again begin by first taking a look inside the main function:
This looks similar to the last binary, however, we can see that the create_password() subroutine was removed. A function called check_password() exists and we can see that after the call is returned, r15 is tested. If that register does not contain 0, the code will eventually hit the jmp instruction at 0x445c and will subsequently exit without unlocking the door, so we need to make sure that when the call is returned, r15 contains a non-zero value.
Let's dig deeper and see what's going on inside check_password():
We can see that there are 4 cmp instructions occurring which will compare 8 hard-coded bytes, 2 at a time with 2-byte offsets from r15 (the start of our input in memory). If execution can reach the final cmp instruction, the program will jump over the clr r14 instruction at 0x44ac, which means that when mov r14, r15 is executed, r15 will have a non-zero value (and instead will contain 0x1 which was set by the previous 44a2: mov #0x1, r14 instruction). Once execution is returned back to main(), the subsequent tst r15 instruction will cause the jump to 0x445e to occur, which will print the access granted message and proceed to unlock the door.
Let's grab those 8 hard-coded bytes and try it out. Don't forget that MSP430 byte pairs are little-endian, so we'll need to reverse the byte order.
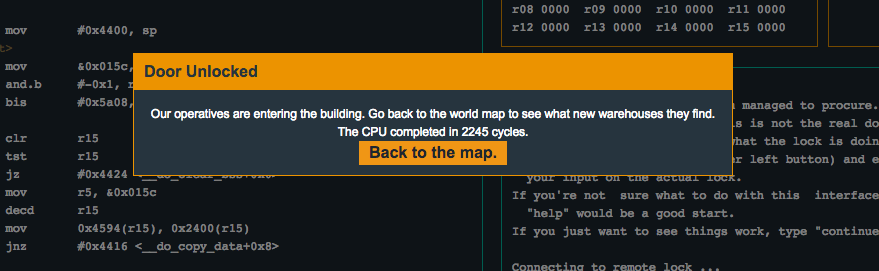
362253555d593356